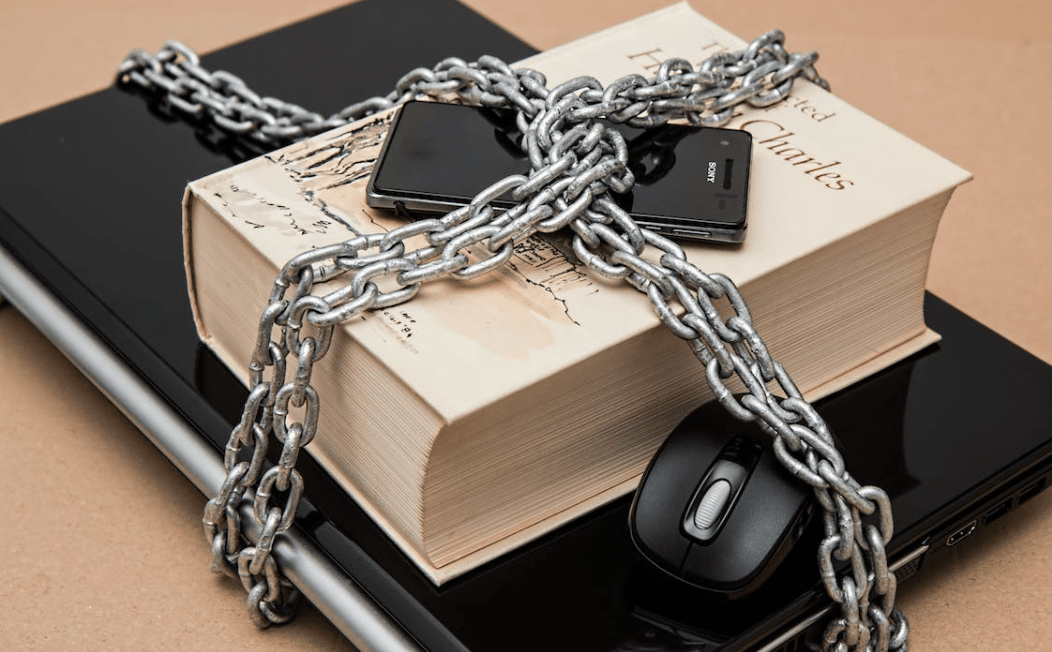
The access request process is a crucial part of the identity lifecycle.
But the cumbersome and time-consuming process of executing these tasks can be a burden on IT teams, especially when they have to deal with hybrid ecosystems or manual processes.
This is why many organizations are trying to automate their access request management and fulfillment activities as much as possible.
In this article, we walk you through what a typical access request management system entails, the risks it mitigates, and its key features.
What is access request management?
Access request management involves managing and controlling user access to IT resources within an organization. The aim is to set up a workflow process that effectively manages user requests for access to critical components of an organization, including systems, data, and applications.
It mainly helps organizations mitigate the risk of unauthorized access, data breaches, and other security threats. It also helps create a central repository for managing access rights and simplifies the process of granting or revoking access when necessary.
Seeing how complex this process is, doing it all manually will only amount to human errors and more security risks. This is where an access request management tool such as Zluri comes into play that automates the process and simplifies tracking and requesting access. The tool automatically sends access requests to the designated person and streamlines onboarding, offboarding, and role management.
How Access Request Management works
Typically, access request management involves various identity lifecycle activities, including:
- Provisioning
- De-provisioning
- Onboarding
- Data rights
- Access governance rules
- Audit readiness
- Compliance with domestic and international security and privacy regulations
The process is complex, largely manual, and requires high levels of oversight to ensure the right people have the necessary access to the right information at the right time. This is a significant challenge for organizations with many diverse departments and locations, requiring multiple stakeholders to act one by one in order to get things done.
Most access request processes deal with role assignment requests, a common activity that involves reserving and assigning roles to users. Unfortunately, these role assignments can create dangerous privilege creep over time.
In addition, they can lead to a variety of other problematic issues, such as re-granting entitlements that are no longer needed, repeating role assignments for a user (redundancy), or allowing the requester to use the same set of entitlements for another user.
This is why most businesses lean on automated logging of access requests that help them prove compliance with PCI-DSS, HIPAA, SOX, GLBA, or GDPR. They establish accurate audit trails that document exactly who has access to what at any given point in time.
Security risks associated with unmanaged access requests
The Internet offers companies unprecedented opportunities to expand their business operations, but it also provides hackers, disgruntled employees, criminals, and corporate spies with access to company information that could lead to data breaches.
As a result, many organizations fail to properly handle access and data security on their network, opening themselves up to vulnerabilities.
Hackers breaking in
Hackers often covet privileged accounts (admin accounts) and credentials. Once they obtain the credentials, they can perform a broad range of attacks on the network without being detected for weeks or months at a time. They can impersonate employees, access data, and establish ongoing access to company computers and servers.
Employee sabotage
Employee sabotage can cause significant damage to your network, including the mishandling of critical information, resetting administrative passwords, and installing malware.
Malware infestation
Personal devices used by employees, contractors, and even suppliers can act as a security weak point. These devices can be infected with malware, have unpatched vulnerabilities, or contain malicious files that could lead to a data breach. They can also be compromised through phishing and inadequate credentials, leading to far-reaching damage.
Bad actors taking advantage
Bad actors—disgruntled former employees and cybercriminals—can all take advantage of unsecured privileged access to move laterally in your network, corrupt data, and compromise your systems and infrastructure. This is called “privilege creep.”
How Access Request Management can mitigate those risks
A good access request management solution counteracts the effects of the access request process by implementing an inverse process—a process that removes the entitlements from users that no longer need them.
This way, access requests can be a very useful tool for mitigating security risks, but only if they are used properly and efficiently.
It helps businesses adhere to the principles of least privileged access by enabling users to only request the privileges they need. They allow IT to quickly view, certify, grant, and revoke access to sensitive organizational information while enforcing policies on an ongoing basis.
In addition to reducing operational costs, it also helps mitigate security risks by ensuring that only the right people have access to the right data or resources. It can create accurate audit trails that show who was authorized at any given time to access a particular resource and how that authorization changed over time.
Key Features of Access Request Management Systems
User Authentication
A user’s identity is protected with a unique ID, password, or biometric that they must remember and use to log in to the system. They can then perform tasks in a secure environment, avoiding potential security vulnerabilities that can compromise a network or a computer’s sensitive data.
This is why you must choose an access request management system that aids you with end-to-end authentication and authorization services. For example, your system should help you set up a key or passcode-based authentication system and a role-based authorization system.
Role-based Access Control
A role defines the permissions that are granted to a user, such as the ability to edit files or add notes. These permissions can be granted to individual users or groups of users.
Many organizations use this type of access control to ensure that they only give users the permissions they need. This allows them to manage user access with greater efficiency and accuracy, keeping data safe from intruders
Another important component of a good Access Control System is the ability to automate removing privileges that are no longer needed by the user. This can prevent privilege accumulation, which can be dangerous.
Access Request Workflow
Typical access request workflow processes involve controlled assignment of roles and entitlements by users via self-service interfaces. Then, those requests are driven through a series of approval steps, which can be manually or automatically managed.
While most access request processes focus on role assignment, a small number of IGA platforms also have support for granting access to low-level entitlements, such as LDAP groups and operating system privileges. These entities are usually not first-class citizens of the IGA platform and are difficult to define policies and ownership for.
Audit Trail and Reporting
An important part of the automation of these processes is a comprehensive audit trail that keeps track of the history of each request, from when it was submitted to when it was approved. This helps auditors identify issues in the process and provides insight into the success or failure of the access request.
Best practices for implementing access request management
Understanding the needs of your organization: Understanding these needs will help you define a clear set of access policies that address your specific security and compliance requirements.
Defining access policies: Access policies establish a standard for managing access to your company’s computers and information systems. They are a good way to create a consistent security posture that preserves data confidentiality, integrity, and availability.
Choosing the right access request management system: A good system will allow you to easily control user access to your organization’s IT resources while also ensuring audit readiness and data privacy compliance.
Moreover, it will support multiple user roles, entitlements, and privileged access requests. It should also integrate with your IT Service Management (ITSM) software and allow you to route requests intelligently based on business rules. It should also include an auditing capability and a way to report on the effectiveness of your system.
Regular Auditing and Review: Regular auditing and review of access entitlements is a critical component of an effective access request management implementation. This enables you to ensure that your access control system and processes are functioning as designed and that users have access only to the privileges they need for their job.
Level up your business security with access request management
Access request management is a key element of the identity lifecycle. It involves provisioning, de-provisioning, and onboarding users, as well as enforcing data rights, access governance rules, and the least privilege principle.
These processes can be time-consuming, manual, and complex for IT administrators. But there are a few best practices for implementation that can help you streamline the process, lower risks, and mitigate compliance challenges.
Author’s Bio
Deepali is an engineer-turned-freelance writer for B2B SaaS, writing actionable long-form content for marketing, Cybersecurity, and HR-Tech companies. When she’s not writing, she’s engrossed in a cozy murder mystery novel with a cup of hot chocolate!






0 Comments